

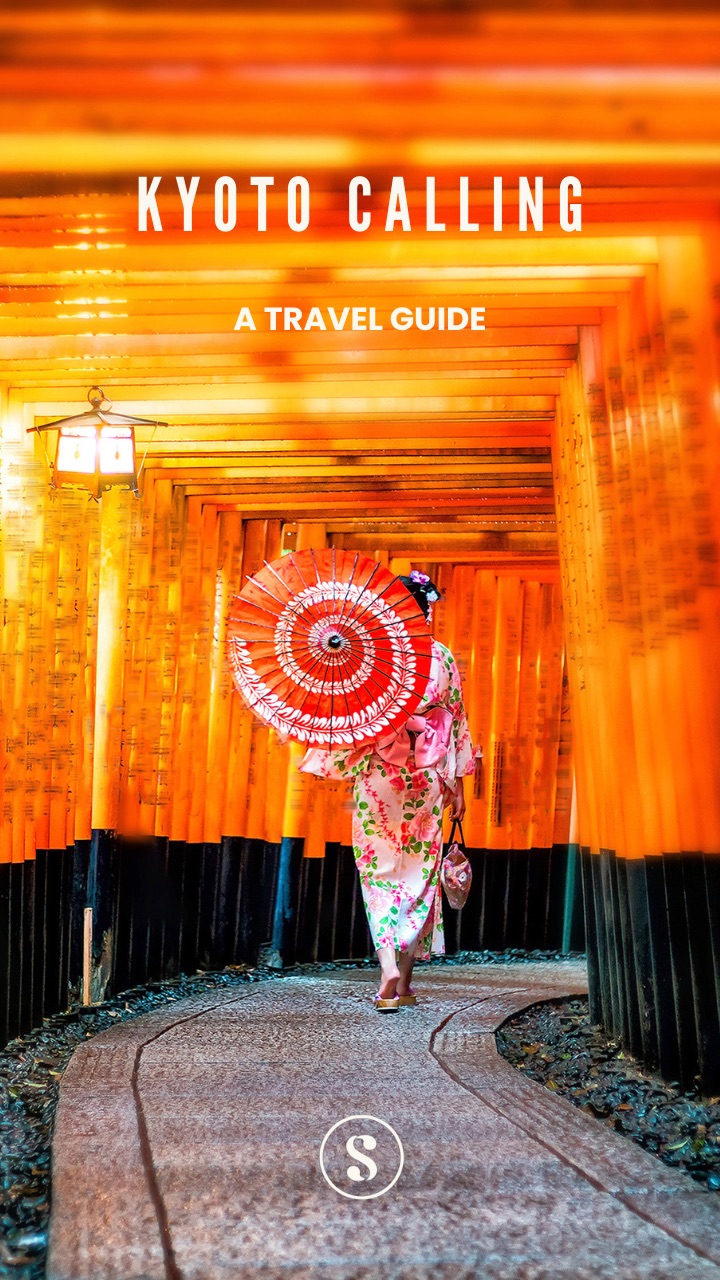
Sign up for Advisory! It’s free and so is our exclusive
welcome
aboard travel guide to Kyoto.
Our weekly goodie bag includes:
What you won’t get: Spam or AI slop!
Already a user ? Login
Privacy Policy. You can unsubscribe any time.Tell us a bit more about yourself to complete your profile.
Thank you for joining our community.



The world’s biggest law firms, powerful governments and companies rely on Indian hackers to do their dirty work for them. No, they are not hiding in the shadows—but hiding in plain sight in shiny offices in Gurgaon and Delhi—as a recent Times UK investigative series reveals.
So how did India become one of the hacker capitals of the world? The answer lies in a company called Appin.
The origin story: Founded in 2004 by Rajat Khare, the Appin Security Group trained people in a variety of skills—including programming and cyber security. It was also an incubator for “white hat” hackers—who would help protect companies and individuals from cyber attacks.
The slide into hacking: By 2010, the company had started a lucrative side business: hacking targets on behalf of governments and corporate clients. Its activities were first exposed in 2013 by a cybersecurity firm called Norman Shark. It is also the first time that India emerged as a possible hub of global hacking—until then the mantra was “It’s always the Chinese.”
Norman Shark found that Appin used more than 600 different websites to distribute their malware and receive stolen information. And its hackers had a worldwide list of targets: Norwegian telecommunications company Telenor ASA, the Chicago Mercantile Exchange, Pakistan's National Disaster Management Authority and China's Tsinghua University.
Most interestingly, this: Among Appin’s listed clients: the Ministry of Defence and the three armed forces. And a number of the listed targets were in Pakistan. But at the time, the government issued a strong denial—and so did Appin—and the ‘evidence’ on Appin itself was plausibly deniable.
Fast forward to 2022: One of Times’ sources references a “homeland security company”: “You are not going to find any details about it over the internet, they work with the Indian government very closely, they do all their offensive [hacking] work.”
And Appin is named as its “training arm”—where the source was trained for a year—and then put to work. He claims that his targets included governments of Turkey, Pakistan, Egypt and Cambodia. The aim was to access secret documents and files in their ministries:
“We were not allowed to have questions. It was just, ‘Hey, this is the target. You have got three months of time. Do whatever you want to do—we need results.’ That’s how it works . . . They will say, ‘Hey, this is the ministry of this particular country, we need this data.’ Our job was to get the data dump and hand it over to the [Indian] agency . . . [The target] can be the external affairs ministry, it can be home, it can be defence, it can be finance. It depends what kind of intelligence they are seeking.”
Soon after the hacking allegations emerged, Appin’s employees “scattered like seeds and set up new firms to utilise their freshly acquired talents in the computer dark arts. This created a more diversified Indian hacking industry.” And by 2020, New Delhi had emerged as the hacking hub of the country. Ethical hacking institutes are dime-a-dozen—offering training and global certification to school and college dropouts.
Say hello to HaaS: or “hacking as a service”—which is the moniker used for this burgeoning industry. Payment is received in bitcoin from clients that range from jealous spouses to parties in a lawsuit and companies looking for dope on rivals. While many are white hat operatives, it’s easy to slip over to the dark side.
One reason: There isn’t as much money in ‘ethical hacking’. While just hacking a single social media account can pay Rs 20,000. The other reason: Indian cyber security researchers are not treated as credible either on the global stage—or in India. Bharat Sanchar Nigam Ltd (BSNL) promptly responded when a French hacker red-flagged a security flaw—after ignoring an Indian cyber security researcher for over a year. As Mint notes, “The lack of respect often drives hackers to take the darker route; money replaces respect.”
One of the most prominent and successful heirs of Appin is BellTroX set up by one of its alums, Sumit Gupta. The company grabbed global headlines in a 2020 Citizen Lab investigation.
The Citizen Lab exposé: In 2020, the Toronto-based organisation revealed the existence of a powerful hack-for-hire group called Dark Basin—and linked it to an Indian company, BellTroX InfoTech Services. It found that Dark Basin had “targeted thousands of individuals and organisations on six continents, including senior politicians, government prosecutors, CEOs, journalists, and human rights defenders.” One of its big projects: phishing attacks on organisations who were part of the #ExxonKnew campaign—which exposed the gas company’s attempts to cover up the effects of its activities on the environment.
Say hello to BelltroX: Sumit Gupta’s first big hacking job was in 2013 for a US diet shake distributor ViSalus—which was embroiled in a lawsuit with its rival Ocean Avenue. The hacking, however, triggered an FBI investigation in 2015—and Gupta was ultimately indicted on charges of hacking, but never arrested. Instead—soon after the ViSalus gig—the 24-year-old set up his own company BellTroX Infotech Services—with the motto “you desire, we do!”
By 2016, he had dozens of employees in his West Delhi office, many of them paid as little as Rs 20,000 a month. But Gupta charged anywhere from a few thousand dollars per account to up to $20,000 for “priority” targets. His most lucrative clients: private investigators hired by companies embroiled in lawsuits. Here’s how it worked:
“Reuters identified 35 legal cases since 2013 in which Indian hackers attempted to obtain documents from one side or another of a courtroom battle by sending them password-stealing emails. The messages were often camouflaged as innocuous communications from clients, colleagues, friends or family. They were aimed at giving the hackers access to targets’ inboxes and, ultimately, private or attorney-client privileged information.”
BelltroX was one of three Indian companies identified by a Reuters investigation—which uncovered a database of more than 80,000 phishing emails sent by Indian hackers to 13,000 targets over a seven-year period.
Say hello to WhiteInt: The Times investigation published this week shows that no single Indian company has a monopoly over black hat hacking. Its reporters went undercover as British corporate investigators looking for hackers for hire—and found plenty of takers in Delhi. They also got access to the client database of a group called WhiteInt—and over 100 of their targets. The company is run from a fourth-floor apartment in Gurgaon—and helmed by 31-year-old Aditya Jain—“an occasional TV cybersecurity pundit who also holds down a day job at the Indian office of the British accountancy firm Deloitte.”
Their targets include everyone from senior journalists to the Swiss president, UK Chancellor and head of European football Michael Platini. Also this: “The gang seized control of computers owned by Pakistan’s politicians, generals and diplomats and eavesdropped on their private conversations, apparently at the behest of the Indian secret services.”
WhiteInt’s most prolific client: A Swiss corporate intelligence company Diligence Global Business Intelligence—which needed help on a “World Cup project.” The assignment for WhiteInt: target anyone who criticised the decision to award Qatar the rights to host the football tournament—or flagged potential FIFA corruption involved (explained in our Big Story here).
Where is Appin today? According to Reuters, several Indian cyber security training outfits still use the Appin name—but there’s no suggestion those firms are involved in hacking.
Where is BelltroX today? Citizen Lab’s revelations “are said to have caused panic in western corporate intelligence circles because so many of the investigators had used Indian companies to hack emails for their clients.” But BelltroX is still in business. Repeated hacking allegations, however, forced Meta to shut down its 400 Facebook accounts.
Where is WhiteInt today? Nothing much seems to have happened other than the fact that Jain lost his Deloitte job.
The bottomline: Our IT economy has always been built around clever tech-savvy Indians doing the heavy lifting for Western clients—at relatively low prices. Why should hacking be any different?
You can check out the two-part Times UK investigation series without a paywall over on the Bureau of Investigative Journalism website. This report is on WhiteInt and the great Qatar hack, while the second details the Times’ undercover sting in Delhi. This 2013 Wall Street Journal report has the first reporting on cyber attacks out of India. Reuters’ investigation looks specifically at how Indian hackers play a dark role in lawsuit battles in the US. Mint lays out why India is the perfect place to become a hack-for-hire hub. We also recommend reading Citizen Lab’s in-depth exposé about Dark Basin. 
Spark some joy! Discover why smart, curious people around the world swear by Splainer!
Sign Up Here!
 souk picks
souk picks